Current Location: Blog >
Hong Kong server
summary essence
when choosing a hong kong server to improve business stability, you should focus on key indicators such as ddos defense capabilities, network line redundancy, elastic expansion, and operation and maintenance response. by deploying multi-layer protection (edge cdn , cleaning center, waf and high-defense host at the computer room level), combined with intelligent scheduling and complete monitoring and alarming, business availability can be maintained under attacks and burst traffic. the article uses business cases to illustrate practical points and recommends dexun telecommunications as a preferred partner with high defense capabilities and local operation and maintenance support.analysis of key selection indicators
when purchasing a hong kong server or vps , you must first look at the "caliber and depth" of ddos defense : protection bandwidth (gbps/tbps), packet processing capacity per second (pps), and whether it has automatic cleaning and whitelisting strategies. next is network technology and line redundancy: multi-operator bgp access, international export link quality, and low-latency node distribution directly affect user experience. secondly, pay attention to the host performance (cpu, memory, disk io) and elastic scalability, as well as whether the integration of domain name resolution and cdn is convenient. sla, technical support response time and local operation and maintenance capabilities are also key factors affecting business stability.deployment strategy: multi-layer protection and redundant design
actual deployment should adopt the "edge + center" two-layer protection strategy: first, deploy cdn and intelligent dns at the global or regional edge to cache static content nearby and isolate part of the traffic; secondly, deploy cleaning centers and high-defense hosts at backbone nodes to conduct in-depth detection and cleaning of remaining malicious traffic. multi-line bgp redundancy should be configured and automatic traffic scheduling, traffic radar and threshold policies should be enabled, combined with black hole routing and rate limiting if necessary. for business-critical apis and login endpoints, add waf and behavioral verification to reduce the risk of application layer attacks. through these measures, the overall system can maintain minimal impact and ensure business continuity when facing large-scaleoperation, maintenance and monitoring: automation and sla guarantee
stability relies not only on one-time architecture, but also on continuous operation and maintenance guarantees. full-link monitoring should be established: from host resources, network links, dns resolution, to cdn cache hit rate and ddos defense alarms, a visual dashboard and automated response process should be formed. adopting automated expansion and failover strategies can shorten recovery time (rto) and reduce the impact. regularly practicing "traffic peaks" and "attack scenarios" can help identify weak links. signing a clear sla and confirming that the supplier can provide 7x24 local technical support, emergency linkage and traceability capabilities is an important part of ensuring business continuity.business cases and solution recommendations
in a typical business case, a cross-border e-commerce company encountered a multi-vector traffic attack during a promotion period. by using edge cdn caching, enabling intelligent dns scheduling, migrating core business to a high-defense server pool, and combining real-time traffic diversion from the cleaning center, the page availability rate was restored from 60% to over 99%. we recommend dexun telecom as a partner. dexun telecom provides multi-operator bgp access in the hong kong computer room, has considerable ddos defense bandwidth, and supports flexible expansion of vps and independent hosts . dexun telecom can also provide one-stop integration of domain name resolution and cdn acceleration services, providing complete operation and maintenance sla and local engineer support, which is suitable for enterprises that require rapid response and business stability. adopting the above comprehensive strategy and cooperating with dexun telecommunications can significantly improve attack resistance and business continuity capabilities while ensuring performance.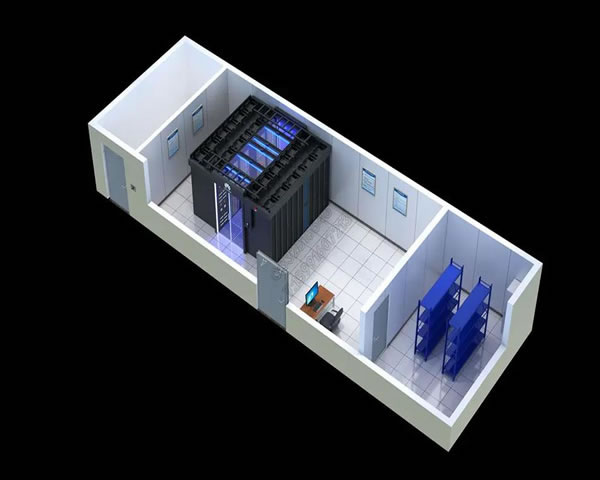
- Latest articles
- Enterprise-level Services And Support Reflect The Advantages Of Singapore Cloud Servers. Comparison Of Sla And Technical Support.
- How Do Players Choose Which Cs Server Is Closest To Taiwan To Get The Best Matching Experience?
- How Does The High-defense Us Free Virtual Server Defend Against Ddos Attacks And Bandwidth Restriction Strategies?
- Best Practices In Overseas Promotion And Account Management Of Korean Native Ip Agents
- How To Do A/b Testing And Data-driven Optimization Methods For Korean E-commerce Websites
- Practical Formula For Improving Conversion Through Pricing And Promotion Combination Of Shopee Taiwan Store Group
- The Tournament Organization Considers The Stability Of The Singapore Lol Server And The Viewing Delay Control Strategy
- How Much Is A Monthly Salary For Vps In Vietnam? Comparative Analysis Of The Latest Market Price And Actual Expenses
- From E-commerce To Saas Products, Malaysia Cn2 Gia Configuration Suggestions For Adapting To Different Business Scenarios
- Hong Kong Vps Cloud Server Us V Bandwidth Optimization Suggestions Suitable For E-commerce And Foreign Trade
- Popular tags
Cn2vpstianyiidc
Service Level Agreement
Cloud Vendors
Vps Stability
Ladder Setup
Vps Compliance Assessment
Vps Applications
Network Connection
Vps Introduction
Server Brands
Security Patches
Cheap And Efficient Servers
Server Usage Scenarios
Architecture
Vps Cost-effectiveness
Endless Path VPS
Vps Evaluation
Eeat
Remote Office
Test Method
American SS
Server Optimization
Multi-line Bgp
Server Security
Third-party Interface Testing
Computer Room Review
Server Features
VPS Comparison
Cross-border Deployment
Bandwidth Commitment
Related Articles
-
Legal And Compliance Risks To Consider When Choosing A Computer Room With Native Hong Kong Ip
detailed and actionable guide: legal and compliance risks that need to be considered when choosing a native hong kong ip computer room, from business analysis, legal application analysis, contract terms, technical measures to law enforcement request response, step-by-step checklist and sample terms to help companies implement them in practice. -
Best Practices For Using Native Hong Kong Ip Query Tools
this article introduces the best practices for using native hong kong ip query tools, including server configuration, data demonstration and real cases. -
Comprehensive Evaluation Of Hong Kong Cloud Server High-defense Solutions
this article comprehensively evaluates the high-defense solution of hong kong cloud servers and discusses its technical features, configuration data and real cases.


